According to a recent eye-opening report by Aqua Nautilus, crucial vulnerabilities exist in the PowerShell Gallery. Consequently, malicious actors and attackers have launched attacks to gain unauthorized access to sensitive information. It’s pertinent to mention that PowerShell Gallery is a widely used repository for managing cloud resources such as AWS and Azure.
Three critical flaws or vulnerabilities have been highlighted in the report. The first flaw revolves around the lax naming module, which allows typosquatting attacks to take place. This enables many more supply-chain breaches, injecting malicious modules into the user’s system.
The second vulnerability involves the manipulation of package metadata. As a result, malicious packages look authentic by imitating the characteristics of famed brands.
The third flaw reveals critical unlisted packages and the sensitive data stored in them. Unsuspecting users are oblivious to the fact that their confidential information has been publicly exposed.
In the report, Aqua Nautilus has issued precautionary guidelines for DevOps and engineers across the globe. According to the recommendations, those developers utilizing PowerShell Gallery must exercise caution and should opt for only signed PowerShell policies related to modules. Another recommendation is to utilize trusted private repositories and implement robust monitoring systems.
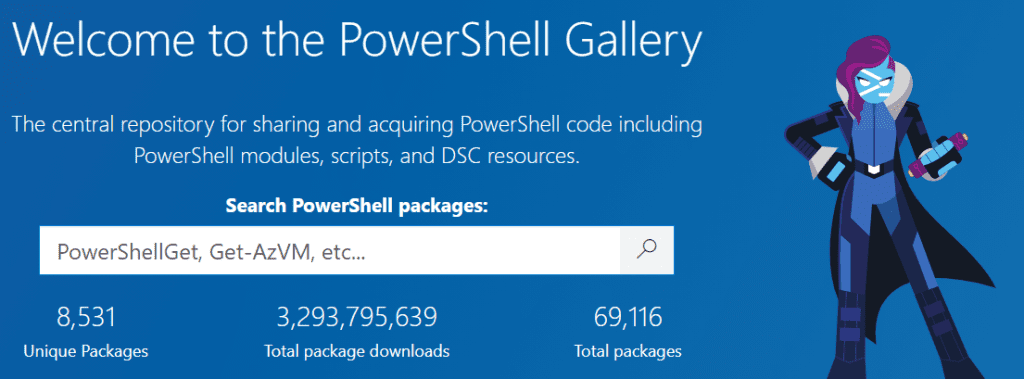
What is PowerShell Gallery?
PowerShell is a renowned command-line shell, and scripting language developed and maintained by Microsoft. Its mainly utilized for automating tasks and system management. Talking about PowerShell Gallery, it is termed the central repository for all the PowerShell content. PowerShell Gallery hosts PowerShell scripts and various other modules of the PowerShell community.
To underline the significance of PowerShell Gallery, thousands of engineers and DevOps use this central repository for cloud deployment and integrating package libraries. Therefore, DevOps engineers must use PowerShell Gallery with security precautions in mind to prevent data leaks.