With the use of digital technology at an all-time high, the protection of online data has become extremely significant. With more than 100 social media platforms available, authentication of users is crucial to ensure unauthenticated users can’t access and misuse someone else’s personal information. As cyber criminals become more intelligent, single-factor authentication is no longer enough to save your data.
Most modern applications use two-factor authentication or, in some cases, multi-factor authentication to allow only authenticated and authorized users to log in. But the question remains, what is the key difference between two-factor (2FA) and multi-factor authentication (MFA)? Read on to find out how 2FA and MFA vary from one another.
What Is Authentication?
When a security system decides whether or not a user trying to log in is legitimate and recognized, this process is called authentication. For example, if a legitimate user A attempts to log in to the system, he will have sufficient evidence (password, pin, security question, fingerprint) that he is indeed User A, and he will be provided access based on that evidence. On the contrary, malicious user B will be locked out of the system. This case study shows the importance of authentication in the protection of data.
The evidence that the user presents to authenticate himself is called a factor of authentication. There are three basic factors of authentication:
1) Knowledge
This authentication factor is basically something that the user knows. This is the most common factor in authentication, including verification through password and pin. Given its simplicity, this factor is the weakest link as hackers attempt to break into a system.
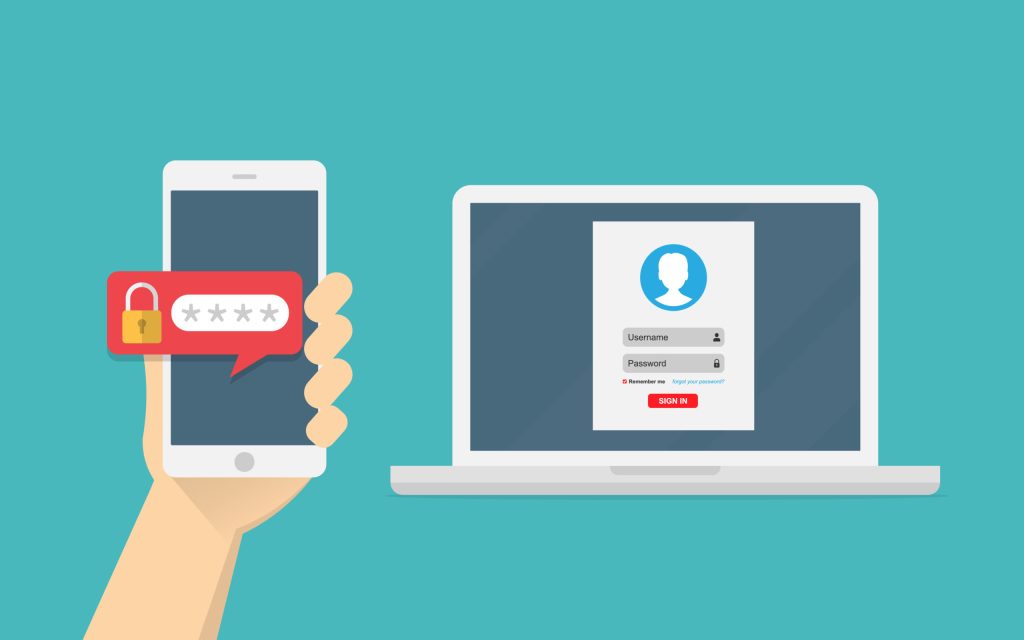
2) Possession
Possession refers to something the user owns, such as tokens, smart cards, and smartphones. Have you tried logging in to your Gmail account only to find that for verification, you have to select the number displayed on the screen on your smartphone? This is a classic example of possession in authentication.
3) Inheritance
Widely considered the strongest of three authentication factors, Inheritance involves an individual’s biometrics like fingerprint or facial recognition. Since a fingerprint is unique to each individual, it is close to impossible for an attacker to break into the system using an authenticated user’s biometrics.
Two-factor Authentication (2FA) vs. Multi-factor Authentication (MFA)
Two-factor authentication, or 2FA, involves exactly two factors of authentication, while multi-factor authentication requires at least two factors, i.e., two or more authentication factors. This means every 2FA is MFA, but every MFA is not 2FA.
In 2FA, there is no restriction on the type of authentication factors to be included. This means that the factors in 2FA can be in the same category. For example, an application requiring an answer to a security question (knowledge) and password (knowledge) is a case study of two-factor authentication.
On the contrary, MFA involves factors that are independent of each other. This means even if MFA consists of only two factors, they cannot be of the same category. A system requiring a user to verify himself via biometric identification (inheritance) in addition to a security passcode (knowledge) is an example of multi-factor authentication.
Another key difference between these two authentication factors is that MFA is more secure than 2FA. The reason is that proving user identity through multiple checkpoints (MFA) instead of simply providing proof of your identity two times (2FA) provides much stronger security. Thus, 2FA and MFA, both are critical for protecting yourself on and off the internet.
Conclusion
In the ever-evolving field of technology, cyber-attacks are a common threat vector. To prevent unauthenticated users from logging into a system or application, different types of authentication mechanisms are prevalent. This blog briefly explained two-factor and multi-factor authentication, highlighting the differences between them.